https://www.itgovernance.co.uk/blog/the-14-cloud-security-principles-explained
The Insider Threat: Strategies to Safeguard Against Malicious Insiders
https://www.itgovernance.co.uk/blog/the-insider-threat-strategies-to-safeguard-against-malicious-insiders
3 ISO 27001:2022 Controls That Help Secure Your Cloud Services
https://www.itgovernance.co.uk/blog/top-5-cloud-security-challenges-risks-and-threats
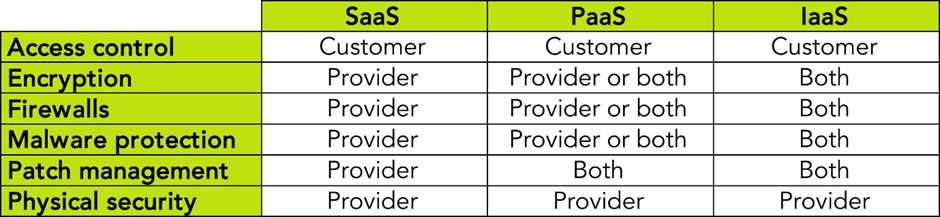
Security Risks of Outsourcing to the Cloud: Who’s Responsible?
https://www.itgovernance.co.uk/blog/security-risks-of-outsourcing-to-the-cloud-whos-responsible
What Are ISO 27017 and ISO 27018, and What Are Their Controls?
https://www.itgovernance.co.uk/blog/what-are-iso-27017-and-iso-27018-and-what-are-their-controls
Cyber Essentials: The 5 Cost-Effective Security Controls Everyone Needs
https://www.itgovernance.co.uk/blog/essential-security-cyber-essentials-and-its-five-controls
How to Address AI Security Risks With ISO 27001
https://www.itgovernance.co.uk/blog/how-to-address-ai-security-risks-with-iso-27001
How Do You Mitigate Information Security Risk?
https://www.itgovernance.co.uk/blog/how-do-you-mitigate-information-security-risk
Where to Start With Cyber Security Risk Management
https://www.itgovernance.co.uk/blog/how-to-manage-your-cyber-risks
GDPR Article 28 Contracts: What You Need to Know
https://www.itgovernance.co.uk/blog/gdpr-article-28-contracts-what-you-need-to-know